Strategic Technical Due Diligence
From Code to Certainty
Trusted Code Base provides deterministic technical audits that translate software risk into valuation clarity, legal defensibility, and deal momentum.
Anatomy of an Audit
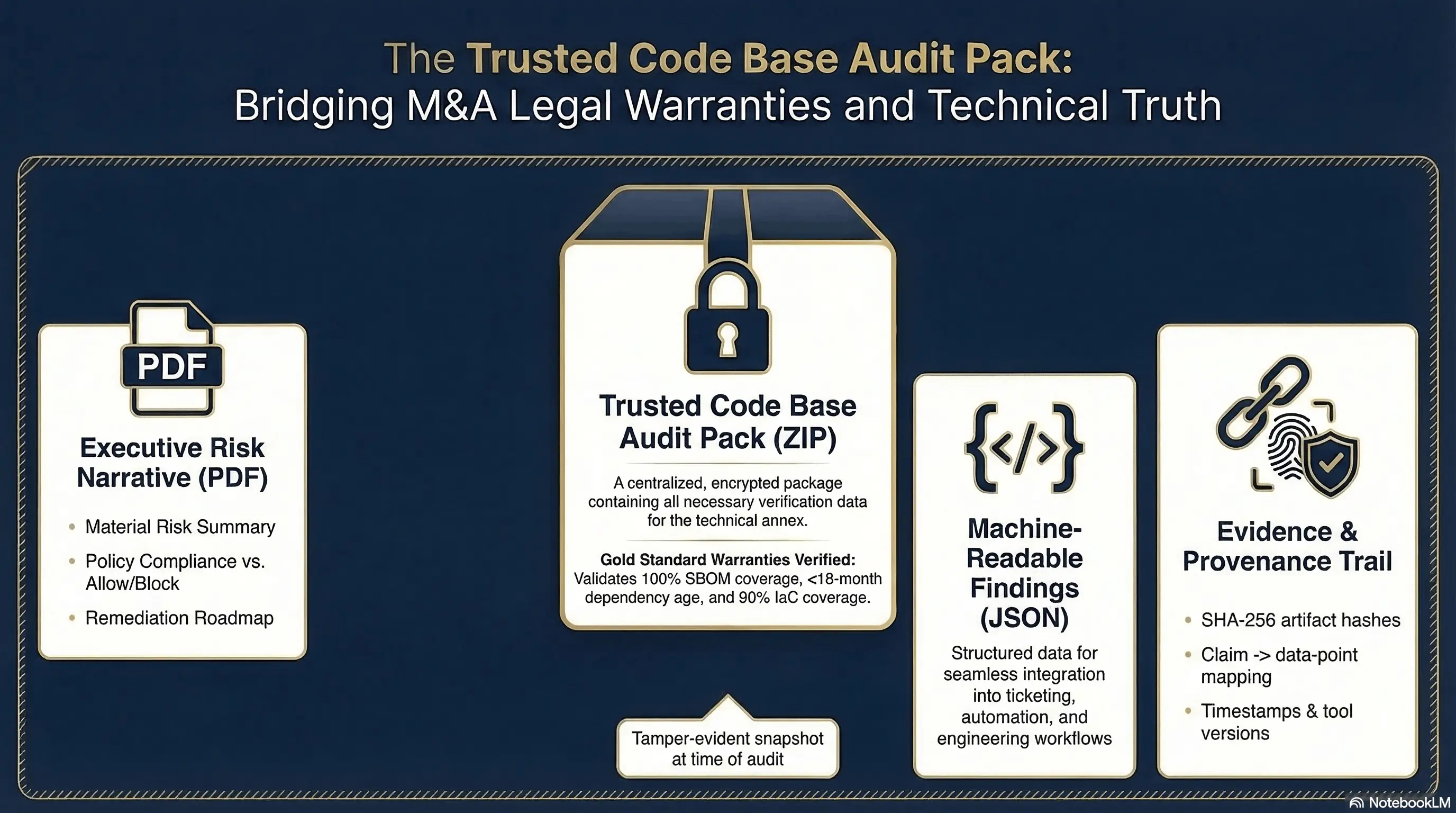
The Trusted Code Base Audit Pack: A Technical Source of Truth
In a high-stakes audit, a login to a dashboard is insufficient. You need a defensible archive that can be shared with legal, technical, and executive stakeholders.
Beyond the Dashboard
The Trusted Code Base Audit Pack is a portable, tamper-evident ZIP file that serves as the canonical record of the software's risk posture at a specific point in time.
- Traceable Evidence: Every insight is backed by evidence, hashes, and provenance.
- Claim Mapping: Each narrative statement maps directly to a machine-readable finding.
- Portable: Share with counsel, executives, and engineering with zero rework.
1. The Executive Risk Narrative (PDF)
This is the "So What?" for the Board and the Deal Team. It avoids technical jargon in favor of business impact.
- Material Risk Summary: A high-level view of risks that could impact valuation.
- Policy Compliance: A direct report on whether the software meets your specific "Allow/Block" criteria.
- Remediation Roadmap: A prioritized list of "Fix Before Closing" vs. "Post-Close" tasks.
2. The Machine-Readable Truth (JSON)
For the engineering team, we provide a canonical JSON report. This data contains the raw findings of our deterministic analyzers, allowing developers to automate the ingestion of our audit results into their internal ticketing systems (Jira, Linear) for immediate action.
3. The Evidence & Provenance Trail
In a legal dispute, "the tool said so" is not a defense. Our Audit Pack includes:
- Artifact Hashes: SHA-256 hashes of every file analyzed (SBOMs, Lockfiles, Bicep files).
- Claim Mapping: Every statement in the PDF Narrative is mapped to a specific data point in the JSON findings.
- Provenance: Timestamps, tool versions, and the exact LLM prompts used for narrative synthesis.
Traceable Evidence
Every claim in the narrative is tied to a source artifact and a cryptographic hash. This ensures that the audit remains defensible for legal, financial, and board-level review.