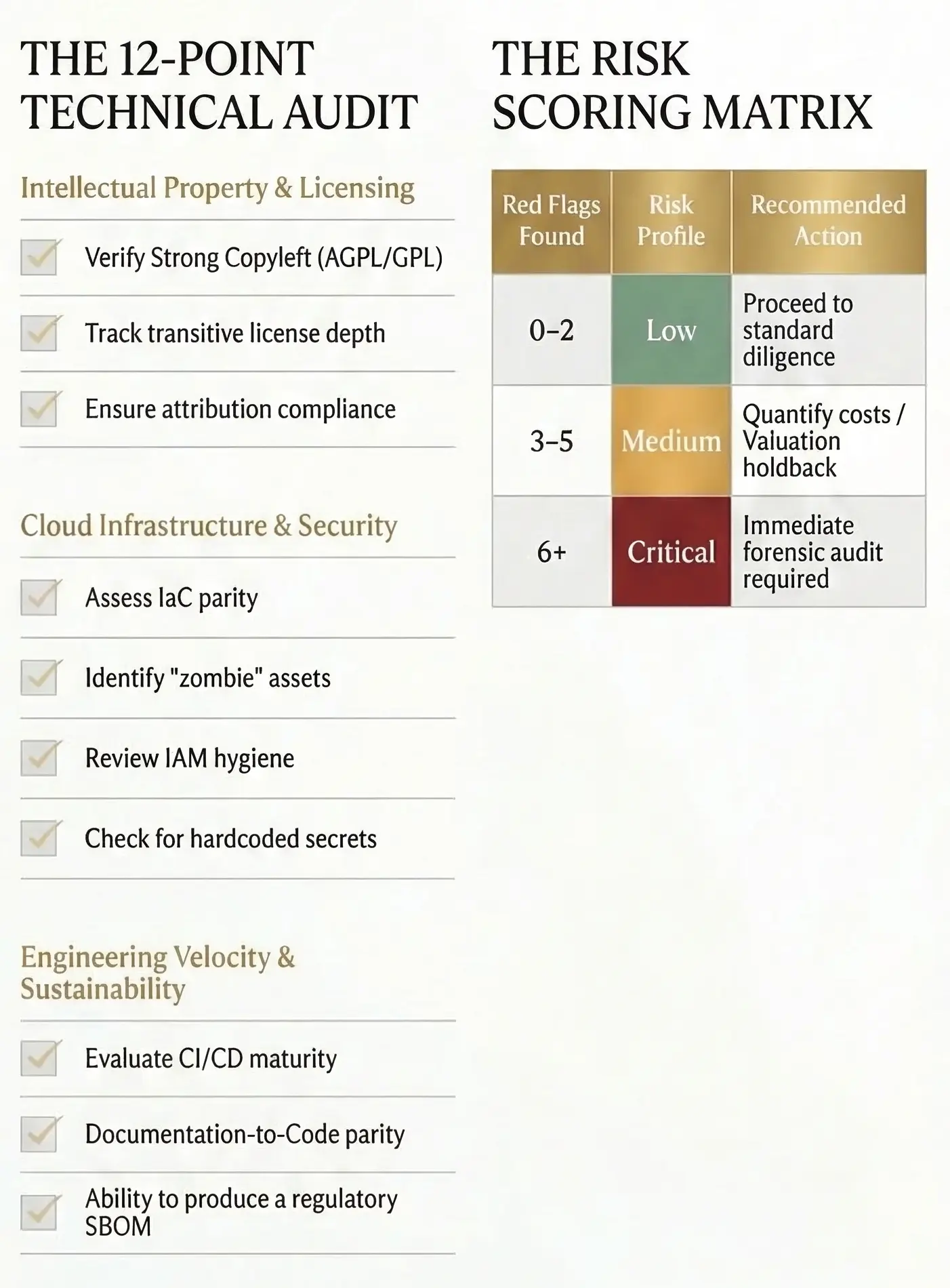
1. The IP Poison Pill: AGPL & Strong Copyleft
Modern software is built on open source, but not all open source is "free." We frequently find AGPL or GPL-licensed libraries integrated into the core proprietary modules of a target company. If the software is delivered as a service (SaaS), this can trigger "reciprocal" obligations, potentially requiring the company to release its entire proprietary codebase to the public. We identify these "poison pills" at the design phase.
2. Infrastructure "Zombie" Liability
Cloud environments like Azure and AWS provide speed, but often at the cost of security. We identify "Owner" level permissions granted to developers at the broad subscription scope—a massive liability for data exfiltration. Furthermore, we audit for "Zombie" infrastructure: public-facing storage buckets and databases with no logging or diagnostics enabled, making a breach both likely and untraceable.
3. The API Design Blindspot
An API is the front door to a company’s data. We audit OpenAPI specifications to ensure that "Write" operations (POST/PUT/DELETE) are strictly authenticated. A common deal-killer is the discovery of "Shadow APIs"—undocumented endpoints that allow unauthenticated access to sensitive PII, representing a catastrophic regulatory risk.